Arun Shrestha, BeyondID CEO & cofounder, has 20+ years in enterprise software with leadership roles at Oracle, Sun, SeeBeyond & Okta.
Cybercrime has evolved. Attackers once hunted for network flaws or brute-forced their way in. Today, they usually just log on. Identity credentials—usernames, passwords, tokens and access rights—are the currency of choice for bad actors.
My company’s research found that identity credential theft now impacts more than 9 in 10 companies, making it the most widespread security problem across industries. Financial services and healthcare are the most frequently breached industries, with the U.S. healthcare sector reporting a breach affecting over 500 individuals nearly every business day, but no sector is immune. Credentials tied to system administrators, executives or single sign-on (SSO) configurations are especially valuable, opening doors to sensitive systems while bypassing firewalls and VPNs.
On underground markets, these identities are traded like commodities, complete with product reviews and refund policies. For companies, the result is billions in losses, rising regulatory exposure and expanding attack surfaces.
Identity Exploit Vectors: How Criminals Get In
Identity exploit vectors (IEVs) are the weak points in identity and access management that attackers exploit again and again. They aren’t exotic zero-days; they’re everyday cracks in enterprise defenses.
Some of the most damaging breaches in recent years have started with a single compromised human account. Analysts have found that the ransomware attack on Colonial Pipeline began with an inactive VPN password that lacked multi-factor authentication (MFA). The breach of Change Healthcare’s 2024 breach seems to have followed a nearly identical script: attackers used stolen credentials to access their system, and the portal was not using MFA.
The problem doesn’t stop with people. Non-human identities—APIs, service accounts and increasingly autonomous AI agents—often carry powerful credentials but receive little oversight.
Federation misconfigurations add another layer of risk. While single sign-on (SSO) improves usability, weak trust setups can collapse and allow outsiders to impersonate insiders. Even secret vaults and shadow identities can become silent backdoors when keys are mismanaged or accounts lack an accountable owner.
Once an attacker breaches the system, they often stay there for a long time. According to IBM’s 2024 Cost of a Data Breach report, breaches that start with stolen credentials last the longest, on average, 10 months before detection. That dwell time gives attackers enormous leverage to escalate privileges, move laterally and monetize access long before defenders even realize they’re inside.
AI: Multiplying Risk And Defense
AI amplifies both sides of the fight.
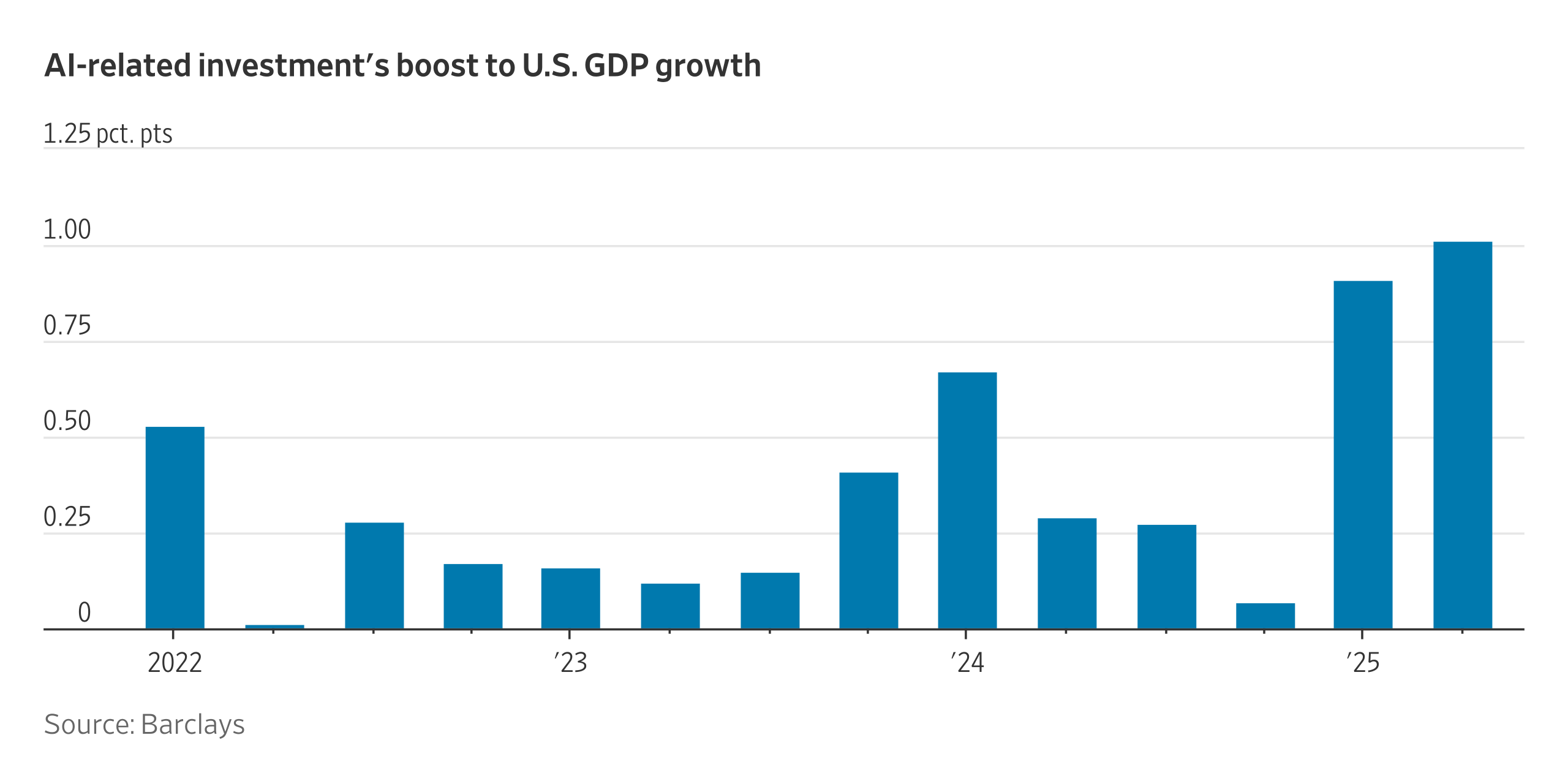
On offense, it makes phishing emails indistinguishable from legitimate messages, automates credential stuffing and accelerates reconnaissance. It also introduces new identities to protect: autonomous agents with their own keys and roles.
On defense, machine learning can baseline normal behavior, spot anomalies in real time and automate the hygiene work security teams rarely have time to finish: disabling dormant accounts, pruning excess privileges and flagging risky access combinations.
The advantage goes to organizations that pair AI-driven detection with disciplined governance: clear ownership for every identity, short-lived credentials and adaptive step-up authentication based on context and risk.
The Leadership Gap
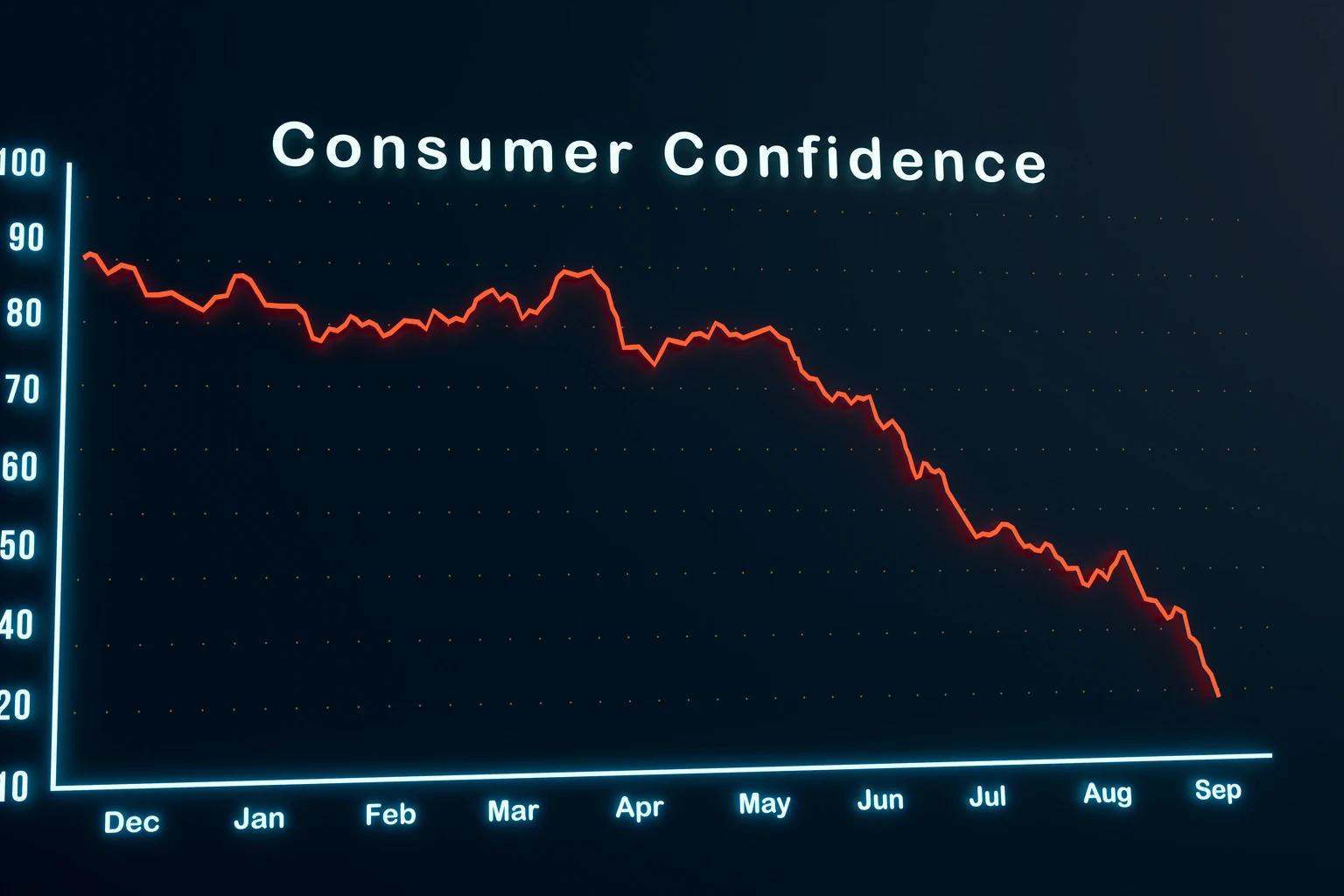
Despite identity being the top attack vector, many boards still treat IAM as a back-office IT concern. While 34% of companies have failed a compliance audit due to identity-related issues, only 6% rank IAM as a top strategic challenge.
Bridging that disconnect requires better communication. Executives respond to business outcomes, not acronyms. Metrics such as privileged account usage anomalies, failed login trends or time-to-revoke access connect identity directly to operational resilience and customer trust.
A Playbook For An Identity-First Approach
The good news: Companies don’t need to boil the ocean. Focus on compounding wins that shrink the most common IEVs:
• Map every identity, human and non-human. Eliminate orphaned and shadow accounts.
• Enforce least privilege. Make high-risk roles just-in-time (JIT) with automatic revocation.
• Harden SSO and federation. Validate tokens rigorously and monitor trust relationships.
• Adopt phishing-resistant MFA. Replace push-spam with passkeys and contextual checks.
• Continuously authenticate. Use behavioral signals to adjust access after login.
• Automate cleanup. Deploy AI/ML to detect anomalies, trim permissions and disable dormant accounts.
• Report identity KPIs at the board level. Frame IAM as enterprise risk, not just IT spend.
From Blind Spot To Blueprint
Cybersecurity has always been a contest of speed and creativity. By focusing on identity, defenders can tilt the field in their favor. Strong IAM defuses the attacker’s most common weapon, reduces dwell time and safeguards trust.
Identity is the economy of modern cybercrime. Treating it as a strategic business priority—funded, governed and measured—gives organizations the leverage they need to stay ahead.
Forbes Technology Council is an invitation-only community for world-class CIOs, CTOs and technology executives. Do I qualify?