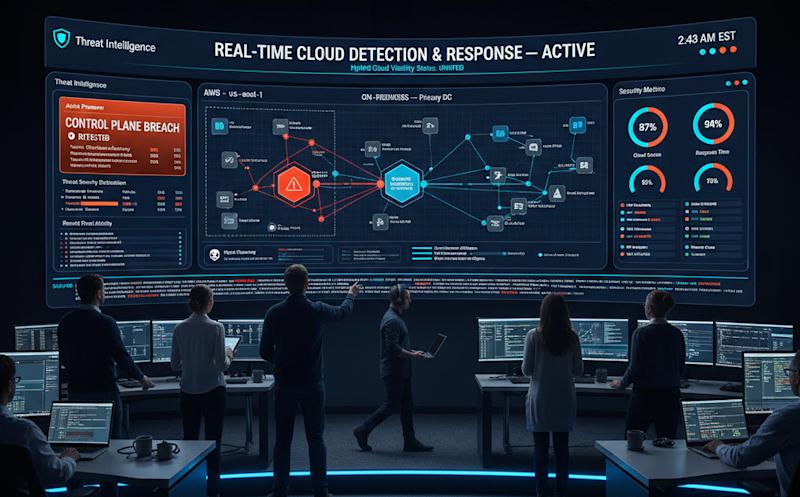
Are Your NHIs in Hybrid Cloud Environments Truly Secure?
Is your organization leveraging the benefits of a hybrid cloud environment while ensuring the security of its Non-Human Identities? NHIs, or machine identities, are increasingly pivotal where organizations shift more operations to the cloud. Yet, this shift presents unique challenges in securing these identities. A deeper understanding of NHIs and their management could be the key to bridging the security gap.
Understanding Non-Human Identities in the Cloud
Where digital interactions are dominated by machines, Non-Human Identities (NHIs) are crucial for maintaining a robust cybersecurity framework. NHIs, essentially machine identities, include encrypted secrets such as passwords, tokens, or keys. These secrets serve as unique identifiers, akin to passports, allowing machines to authenticate and perform tasks. However, without proper management of these NHIs, organizations expose themselves to potential security risks.
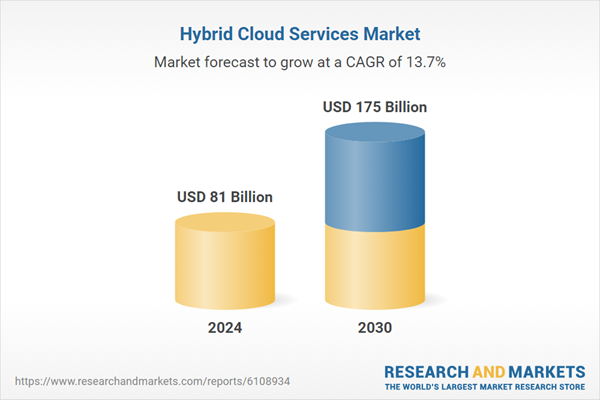
The hybrid cloud environment—where a mix of on-premises, private cloud, and third-party public cloud services are used—presents both an opportunity and a challenge for NHI management. While hybrid clouds offer flexibility and scalability, they also increase the complexity of managing machine identities.
Why NHI Management Is Crucial for Hybrid Cloud Security
The security of NHIs in a hybrid cloud setup involves more than just deploying point solutions like secret scanners. Such tools may provide limited insights, failing to cover the entire lifecycle of NHIs. Instead, a comprehensive NHI management strategy ensures end-to-end protection, addressing everything from discovery and classification to threat detection and remediation.
The importance of this holistic approach is underscored across various domains, particularly in industries heavily reliant on cloud infrastructure, such as:
- Financial Services: Protecting client data and financial transactions from unauthorized access.
- Healthcare: Safeguarding sensitive patient information and complying with stringent regulations.
- Travel: Ensuring secure access to real-time travel data and services.
- DevOps and SOC Teams: Providing a secure pipeline for continuous integration and deployment.
Key Benefits of Effective NHI Management
When organizations adopt a strategic approach to managing NHIs, they can realize several advantages:
- Reduced Risk: Proactively identifying and mitigating security risks lowers the likelihood of breaches and data leaks.
- Improved Compliance: NHI management helps meet regulatory requirements, ensuring policy enforcement and maintaining audit trails.
- Increased Efficiency: Automating NHIs and secrets management frees up security teams to concentrate on strategic initiatives.
- Enhanced Visibility and Control: Providing a centralized view of access management and governance.
- Cost Savings: Automating critical processes like secrets rotation and NHIs decommissioning reduces operational costs.
With cybersecurity experts emphasize, managing NHIs is not just about protecting machine identities but ensuring these identities have controlled access to necessary resources. The analogy of NHIs as tourists with passports is fitting—ensuring these “tourists” have only the permissions they need prevents potential abuse or mishaps.
Strategic Insights into NHI Security Management
The strategic importance of NHI management transcends typical IT operations. Consider an organization that experiences frequent password reset requests or unauthorized access attempts due to poorly managed NHIs. Such instances not only disrupt operations but also increase vulnerability to malicious attacks. A proactive NHI management strategy involves continuous monitoring and analysis of NHIs, detecting anomalies in their behaviors, and responding swiftly to threats.
Moreover, as noted in Non-Human Identities Security in Healthcare, maintaining an updated inventory of secrets and monitoring their access permissions are vital steps in safeguarding critical data. This ensures that no secret or NHI falls through the cracks, thus bolstering the overall security posture.
Building a Secure Hybrid Cloud Environment
Organizations must foster a collaborative environment between their security and R&D teams. This collaboration ensures that security measures are not only developed but are aligned with the organization’s R&D activities. Additionally, integrating NHI management within the larger security framework is essential, as highlighted in Keeping Security in Stride: Why We Built Entro’s Third Pillar for Agentic AI.
For organizations embarking on or currently navigating their hybrid cloud journey, implementing robust NHI management practices is non-negotiable. By doing so, they not only protect their assets but also position themselves as leaders.
Innovative Practices for NHI Management
Organizations must adapt to changing by adopting innovative practices. This includes leveraging AI and machine learning for predictive analysis and threat modeling, ensuring that NHIs are not just protected but capable of adapting to emerging threats.
The integration of automation technologies into NHI management processes is another critical innovation. By streamlining routine tasks, such as secrets rotation and access management, organizations can reduce manual errors and enhance efficiency.
With the digital transformation continuing to evolve, the role of NHIs in cybersecurity becomes even more critical. Organizations that invest in comprehensive NHI management are better equipped to tackle the challenges of today and tomorrow.
The journey to secure hybrid cloud environments begins with understanding and managing NHIs effectively, ensuring that machine identities remain secure and functional.
Advancing the Security of NHIs in Hybrid Cloud Systems
Have you ever wondered what role non-human identities (NHIs) play in your hybrid cloud environment? When we unpack the complexities of securing NHIs, the core understanding needed is not just about protecting machine identities but ensuring their interactions within your system are securely managed.
Tackling NHI Security Challenges in Hybrid Cloud
Hybrid cloud systems, while offering remarkable agility and efficiency, introduce complex security challenges, especially when it comes to managing NHIs. Where organizations continue migrating to these environments, the challenge is often how to maintain control over the myriad of machine identities that are created and destroyed dynamically. Given their vital role, if machine identities are compromised, they could lead to unauthorized access or data breaches, thwarting the cloud’s benefits entirely.
NHI management in such environments requires a more strategic approach due to multiple factors, including the dynamic nature of hybrid clouds and the variety of technologies they encapsulate. The need has never been more pressing for advanced solutions that not only manage but anticipate potential threats associated with NHIs.
Balancing Security and Accessibility
One of the keys to effective NHI management is finding the balance between security and accessibility. Organizations often face the dilemma of enforcing stringent security measures that could hinder the speed and fluidity that cloud services confer. However, by centralizing NHI management, organizations can streamline control over secrets and machine identities without compromising on security or efficiency.
Discussing such balancing acts leads us to explore how DevOps and SOC teams can cooperatively operate to maintain this equilibrium. By closely cooperating, these teams ensure that continuous integration and deployment processes do not inadvertently create security gaps.
Automation and Efficiency in NHI Management
Automation is a critical component in modernizing the management of NHIs. By automating key processes such as secrets rotation and the decommissioning of obsolete identities, organizations can drive down operational costs and reduce the window for human error—common during manual handling of machine identities.
Consider for a moment a large healthcare provider managing vast datasets across a hybrid cloud environment. Through automation, they can efficiently manage NHIs to safeguard sensitive patient data and ensure compliance with data protection regulations.
The intricacies of automation also allow security teams to handle increased NHI workloads effortlessly, scaling with business needs and providing improved response times—a significant advantage in fast-paced cloud environments.
Proactive Threat Monitoring and NHI Security
Proactive threat monitoring involves the continuous analysis of machine identity behaviors, using tools that can spot unusual patterns signaling potential security incidents. This form of threat detection, akin to vigilantly monitoring a crowded crowd for suspicious activity, is where AI and machine learning show their true value.
Artificial Intelligence (AI) becomes a defense partner when it assists in:
- Detecting anomalies by analyzing historical data to set benchmarks for normal machine behavior.
- Predicting possible security infractions using threat intelligence feeds combined with behavioral analytics.
- Guiding automated responses to detected threats, allowing immediate containment actions, reducing potential damage.
Incorporating these intelligent systems transforms NHI management from a reactive to a proactive stance, enhancing the organization’s overall security posture significantly.
Expanding the Perspective: Collaborative Security Approaches
Ensuring robust NHI security also involves broadening the conversation beyond the technical sphere to include strategic and operational considerations. It’s crucial for organizations to align their security goals with business objectives, ensuring the whole ecosystem works towards a unified goal.
Fostering a culture of collaboration between R&D, IT, and security teams is instrumental. These interdepartmental connections help create seamless transitions from development to deployment, embedding security into the lifecycle of NHIs naturally. This is reflected in an Incident Response Plan that involves coordination across all organizational levels to swiftly handle any threat encounters.
Thoughts on NHI Management
The heightened focus on NHI management not only leads to fewer breaches but inspires confidence in leveraging cloud technologies robustly. When we’ve explored, implementing a comprehensive NHI management strategy can dramatically transform an organization’s security proactively guarding against vulnerabilities while ensuring operational efficiency.
Evolving technologies like AI and automation will continue to shape the security strategies around NHIs, steering organizations toward more intelligent, dynamic, and adaptive security infrastructures. To thrive in competitive environments, organizations must not only adopt these innovative strategies but continually refine them, ensuring their machine identities remain secure amidst evolving threats.
The pressing nature of these challenges highlights the importance of perpetual vigilance and adaptation in NHI security. A secure hybrid cloud environment becomes a fortress when NHIs are not merely managed but strategically empowered.
Thus, through streamlined, collaborative, and proactive NHI management, organizations can continue to leverage the profound benefits of cloud technologies without compromising their security.
The post How Safe Are Your NHIs in Hybrid Cloud Environments? appeared first on Entro.
*** This is a Security Bloggers Network syndicated blog from Entro authored by Angela Shreiber. Read the original post at: https://entro.security/how-safe-are-your-nhis-in-hybrid-cloud-environments/